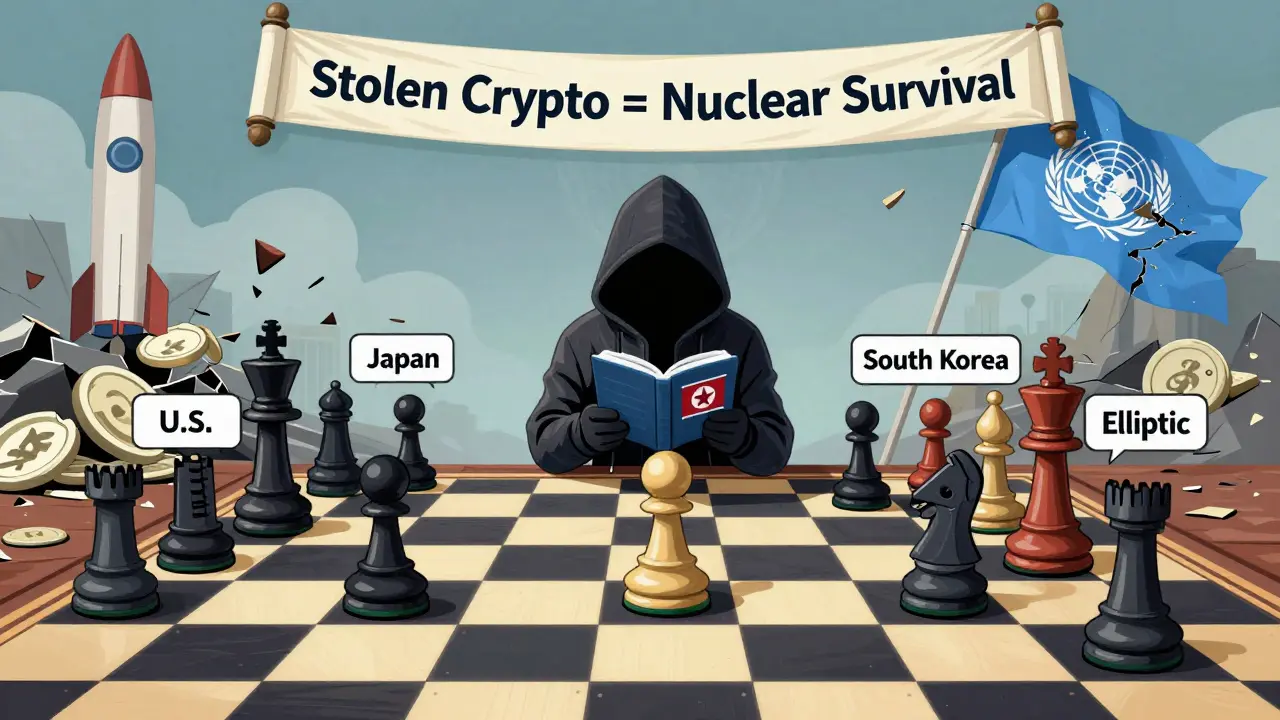
North Korean Crypto Sanctions and Sanctioned Wallet Addresses: How the Regime Funds Its Weapons with Stolen Digital Assets

Since 2017, North Korea has turned cryptocurrency theft into a state-run industry. It’s not random hacking. It’s systematic, well-funded, and directly tied to the regime’s nuclear weapons program. By 2025, the Democratic People’s Republic of Korea (DPRK) had stolen over $2.03 billion in digital assets - the highest annual total ever recorded. That’s more than triple what was stolen in 2024. And this isn’t just about money. This is about survival. Every stolen Bitcoin, Ethereum, or Solana is being converted into weapons-grade materials, missile parts, and military technology that bypasses international sanctions.
How North Korea Steals Cryptocurrency
North Korea doesn’t break into wallets with brute force. They use a mix of social engineering, malware, and targeted attacks on exchange platforms. The biggest heist in 2025 was the $1.46 billion breach of Bybit, one of the world’s largest crypto exchanges. That single attack accounted for nearly 70% of all DPRK-linked thefts that year. Other targets included LND.fi, WOO X, and Seedify - platforms that offered high liquidity and weak security controls.
These aren’t one-off incidents. Elliptic, a blockchain analytics firm, tracked over 30 separate hacks in 2025 that were directly linked to North Korean hacking groups. The pattern is clear: go after exchanges with thin liquidity layers, exploit vulnerabilities in cross-chain bridges, and move quickly before defenses can react. Their teams work like military units - with specialized roles for reconnaissance, exploitation, laundering, and extraction.
What makes them dangerous is their adaptability. When one platform improves security, they shift focus. When centralized exchanges tighten controls, they target decentralized finance (DeFi) protocols. The February 2025 Bybit breach showed they’ve mastered how to exploit the gap between centralized custody and decentralized infrastructure. And they’re already testing new methods - targeting lending platforms, yield aggregators, and liquidity pools in 2026.
From Stolen Coins to Missiles
Stolen crypto doesn’t stay in wallets. It gets laundered. And North Korea has perfected the art of turning digital assets into real-world weapons funding.
Their laundering process is complex. First, stolen coins are moved through multiple wallets - sometimes dozens - to break the trail. Then, they use mixers and tumblers to obscure transaction histories. After that, they convert large amounts into privacy coins like Monero or Zcash, which are nearly impossible to trace. Finally, they swap those into stablecoins, then into fiat currency through offshore exchanges or unregulated OTC traders in Southeast Asia.
According to the Multilateral Sanctions Monitoring Team (MSMT), which includes the U.S., Japan, South Korea, and eight other nations, this entire pipeline is coordinated by state-run entities. One such group is Chinyong Information Technology Cooperation Company. Another is Korea Sinjin Trading Corporation. These aren’t random hackers. They’re government contractors paid to steal, launder, and deliver funds.
The end result? Cash. And that cash buys uranium, rocket fuel, missile guidance systems, and components for nuclear warheads. The U.S. Treasury Department confirmed in July 2025 that North Korea’s cyber operations are now the regime’s primary source of foreign currency - surpassing even arms sales and illegal drug trafficking.
Sanctioned Wallet Addresses: What We Know
You won’t find a public list of every North Korean crypto wallet. That’s intentional. If the addresses were published, the regime would just create new ones. But U.S. Treasury’s Office of Foreign Assets Control (OFAC) has sanctioned dozens of wallet clusters linked to DPRK operations.
These aren’t single addresses. They’re clusters - groups of wallets that show identical transaction patterns, timing, and movement behaviors. Elliptic’s analysis identifies these clusters by tracking how stolen funds move. For example, if 12 different wallets all send funds to the same mixing service within 48 hours, and then those funds exit to the same exchange, it’s likely a single operation.
OFAC has publicly named entities tied to these clusters: Vitaliy Sergeyevich Andreyev, Kim Ung Sun, and Shenyang Geumpungri Network Technology Co., Ltd. These are not names you’ll find on a corporate website. They’re fronts. Real people? Maybe. Or they’re aliases used by state operatives.
The U.S. government doesn’t publish full wallet lists. But exchanges and compliance firms use blockchain analytics tools to screen against these clusters. Major platforms like Binance, Coinbase, and Kraken now flag any transaction that touches a known DPRK-linked address. The system isn’t perfect - new clusters emerge daily - but it’s forced North Korea to spend more time and resources laundering each dollar.

Why Sanctions Are Hard to Enforce
Sanctions sound simple: freeze assets, block transactions, cut off funding. But crypto makes this nearly impossible.
First, there’s no central authority. Unlike banks, there’s no global regulator overseeing crypto transactions. A wallet can be created in seconds, anywhere in the world, with no ID required.
Second, North Korea uses third-party intermediaries. They don’t send stolen coins directly to a weapons supplier. They send them to a front company in Vietnam, then to a Cambodian OTC trader, then to a Chinese underground bank. Each step adds layers of obfuscation.
Third, they exploit regulatory gaps. Some countries still don’t require crypto exchanges to collect KYC data. Others lack the technical capacity to monitor blockchain activity. North Korea targets those jurisdictions.
Even when a wallet is flagged, it’s not frozen. Only the U.S. and a few allied nations can legally block transactions. In most countries, the funds just pass through untouched.
The Global Response
The international community isn’t sitting still. The MSMT, formed in 2024, is the most coordinated effort yet. It’s not a UN body. It’s a coalition of 11 nations working together to share intelligence, track transactions, and pressure non-compliant jurisdictions.
The U.S. has taken the lead. In July 2025, they offered up to $15 million for information leading to the disruption of North Korea’s crypto operations. That’s not just a reward. It’s a signal: we’re serious, and we’re looking everywhere - from hackers in Russia to exchange operators in the Philippines.
Japan and South Korea have tightened their own rules. Exchanges in both countries now require real-time monitoring of incoming and outgoing crypto flows. They’ve also increased penalties for non-compliance. In 2025, three South Korean exchanges were fined over $20 million for failing to block DPRK-linked transactions.
But the real shift is in technology. Blockchain analytics tools are now standard for any serious crypto business. Companies like Chainalysis, Elliptic, and TRM Labs provide real-time alerts on DPRK-linked activity. These tools don’t just detect known addresses - they predict new ones based on behavioral patterns. That’s how they caught the Bybit breach before it was fully exploited.
What’s Next in 2026?
North Korea won’t stop. They can’t. Their economy is collapsing. Sanctions are biting. Crypto theft is their lifeline.
Expect more attacks on DeFi protocols. The $1.46 billion Bybit hack was a turning point - it showed they could hit a major exchange and walk away with billions. Now they’re studying how to exploit liquidity pools, automated market makers, and cross-chain bridges.
They’re also investing in new tools. Reports suggest they’re developing their own privacy-focused blockchain to hide transactions even better. They’re hiring blockchain developers from Eastern Europe and Southeast Asia. They’re training new teams in AI-driven transaction analysis.
The good news? The tools to stop them are getting better. More exchanges are adopting blockchain screening. More governments are sharing data. More regulators are demanding compliance.
The bad news? The race isn’t over. North Korea has shown it can adapt faster than anyone expected. And as long as there’s a way to turn stolen crypto into weapons, they’ll keep trying.
Why This Matters to Everyone
You might think: ‘This is a North Korea problem. It doesn’t affect me.’ But it does.
Every time North Korea steals $100 million, it weakens trust in crypto. Exchanges lose money. Users lose confidence. Prices drop. Regulations tighten. Legitimate projects get caught in the crossfire.
More importantly, these funds are directly funding weapons that threaten global security. A missile developed with stolen Bitcoin could be aimed at a U.S. base, a Japanese city, or a South Korean port. This isn’t just about finance. It’s about national defense.
The fight against North Korean crypto theft is one of the most critical cybersecurity battles of our time. It’s not about stopping hackers. It’s about stopping a regime that’s willing to risk global war for survival.
Are there public lists of North Korean crypto wallet addresses?
No, there are no official public lists. The U.S. Treasury and other agencies identify wallet clusters linked to North Korea, but they rarely publish exact addresses. This is done intentionally to prevent the regime from easily changing their addresses. Instead, blockchain analytics firms like Elliptic and Chainalysis use behavioral patterns to detect and flag suspicious activity in real time. Exchanges use these tools to screen transactions, but they don’t share their full watchlists.
How does North Korea turn stolen crypto into weapons?
North Korea uses a multi-step laundering process. Stolen crypto is moved through dozens of wallets to break the trail, then converted into privacy coins like Monero. These are swapped into stablecoins, then cashed out through unregulated OTC traders in countries like Vietnam, Cambodia, or Laos. The cash is then used to purchase materials like uranium, graphite, and rare earth metals - components needed for missiles and nuclear devices. These purchases are often made through front companies in China and Russia.
Can blockchain analytics fully stop North Korean crypto theft?
No, but it’s the best tool we have. Blockchain analytics can detect known patterns and flag suspicious behavior, but North Korea adapts quickly. They change their methods every few months - switching platforms, using new mixers, or exploiting gaps in DeFi protocols. The goal isn’t to stop every theft - that’s impossible - but to make it expensive, slow, and risky enough that the regime can’t scale its operations. Every delay, every failed transaction, adds pressure.
Why hasn’t the UN done more to stop this?
The UN has passed multiple resolutions banning North Korea’s crypto activities, but enforcement is weak. Only a handful of countries have the technical capability and political will to monitor blockchain transactions. China and Russia have blocked stronger UN action, citing sovereignty concerns. As a result, enforcement is fragmented. The Multilateral Sanctions Monitoring Team (MSMT) - formed by the U.S., Japan, South Korea, and others - is now the most effective body tracking these crimes, but it’s not a UN agency and lacks enforcement power.
What can regular crypto users do to avoid supporting North Korean operations?
Use only regulated exchanges that perform blockchain screening. Avoid using privacy-focused services like mixers or tumblers unless you fully understand the risks. Never send crypto to unknown wallets, especially if the transaction comes from a high-risk jurisdiction. If you’re using DeFi platforms, check whether they integrate tools like Elliptic or TRM Labs to screen for sanctioned addresses. Most importantly, report suspicious activity - many exchanges have whistleblower channels, and the U.S. offers up to $15 million for credible tips.

Austin King
This is terrifying but also kind of fascinating. The fact that they've turned crypto theft into a state-run industry is insane. I don't think most people realize how much of a lifeline this is for them. Every time they pull off a heist, it's not just money - it's another missile.
Bryanna Barnett
yasss queen 🙌 they really out here turnin btc into nukes like it's a side hustle lmao
Rachel Rowland
I've been following this for years and honestly the most chilling part isn't the scale of the theft - it's how systematic it is. They don't just hack. They plan. They train. They adapt. And they have teams dedicated to laundering, not just stealing. This isn't some rogue hacker group. It's a full-on cyber warfare division with a budget. We need to treat it like one.
Bonnie Jenkins-Hodges
AMERICA WE HAVE TO DO SOMETHING 🇺🇸🔥 THEY'RE USING OUR MONEY TO BUILD NUKES 😡
Cerissa Kimball
The laundering pipeline described here is remarkably sophisticated. The use of privacy coins as an intermediary layer followed by stablecoin conversion and OTC cash-out via Southeast Asian intermediaries demonstrates a high level of operational discipline. The geopolitical implications are profound and warrant urgent multilateral coordination
Jeffrey Dean
You know what's funny? We act like this is some new threat. But this is just capitalism with nukes. They're exploiting the same system we built. The real crime isn't the theft - it's that we let crypto become a black market for nation-states. We made the hole. They just dropped the shovel in.
Olivia Parsons
I'm curious - how do they even get paid? Like, if you're a hacker working for them, do they send you crypto? Or do you get cash in a suitcase?
Nick Greening
Oh please. This is all just fear porn. North Korea steals crypto? So what. China and Russia do way worse and nobody calls them terrorists. Why is it always the bad guy with the funny hat?
Jackson Dambz
The entire premise of this article is built on unverified claims from Elliptic and OFAC. These are private firms with clear political agendas. There's zero peer-reviewed evidence that any of these wallet clusters are definitively tied to the DPRK government. It's all correlation dressed as causation.
Jesse VanDerPol
They're not just stealing. They're learning. Every time a platform patches a vulnerability, they study it. Every time a new DeFi protocol launches, they test it. This isn't random. It's a feedback loop of exploitation. And we're not keeping up.
jonathan swift
I know what's really happening. This is all a psyop by the deep state to justify more surveillance. The 'stolen crypto' is fake. The wallets are planted. They want you scared so you'll give up your privacy. Wake up. They're not stealing - they're framing.
Datta Yadav
Let me break this down for you. The entire narrative is built on a foundation of Western bias. North Korea is not some rogue state - it's a sovereign nation defending itself against imperialist sanctions. The crypto theft is a form of asymmetric resistance. The real villain here is the U.S. dollar hegemony and the global financial system that excludes them. This isn't crime - it's survival. And frankly, I admire their ingenuity. They're playing 4D chess while we're still stuck on checkers.
Lydia Meier
The data presented lacks transparency. No primary sources. No methodology for how Elliptic attributes transactions to DPRK. No peer-reviewed validation. This reads like a press release from a compliance vendor.
Basil Bacor
bloody hell this is wild. i thought crypto was supposed to be decentralized but turns out its just a new way for dictators to rob banks 😂
Leah Dallaire
What if the real threat isn't North Korea - but the fact that we're allowing blockchain analytics firms to act as global police? Who owns Elliptic? Who funds Chainalysis? Who decides what's 'sanctioned'? We're building a surveillance state on public ledgers. And we call it security.
prasanna tripathy
I'm from India and honestly this is the first time I've seen crypto used like this. It's scary but also kinda brilliant in a twisted way. They're using tech we all love against the system that tried to isolate them. I don't agree with what they're doing... but I get why they're doing it. The world is unfair. And they found a loophole.